Phishing – and we’re not talking fish!
We’re talking about the most frequent and easy to fall for cyber attack.
Phishing is a type of attack that most commonly uses email or messaging services (via text message or phone calls) to fool you into taking an action you should not take. The sender pretends to be a trustworthy source/contact/organisation — like a client, a bank or government agency — in an attempt to get you to provide them with login credentials, personal information or particularly financial details.

What information are they Phishing for?
- Usernames and passwords for your online accounts, including social media accounts
- Personal information and documents such as drivers’ licenses and passports
- All or portions of your banking details
- Your credit card details
Tips for spotting Phishing emails:
Here are some basic rules to follow to help protect yourself.
- You don’t recognise the sender or the name of the company
- The sender’s name doesn’t look quite right
- The details in the email are nothing to do with your role
- The email addresses you in a strange way – Dear Sir, Dear Madam, Dear you
- There is a request with a sense of urgency
- The email contains bad grammar
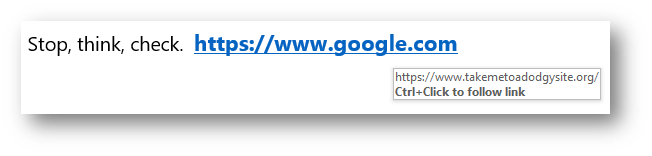
- If the email directs you to click a link, hover over the link with your mouse. The address that you see doesn’t match the location it says it is taking you to (see image below).
Good habits when dealing with emails:
- Be cautious about emails asking you to verify or update your details online by following a link in the email.
- Be cautious of emails saying you have won prizes from competitions you don’t remember entering.
- Don’t click on web links from someone you don’t know.
- Use bookmarks, favourites or use google to get to websites rather than using the links in the email.
- If you’re not sure about the content, contact the person you think might have sent this email. Use your own stored contact details, not those included in the email.
How to react to phishing attempts:
In most cases, the act of opening and reading an email is fine. For a phishing attack to be successful, the cyber criminals need to trick you into performing an action.
- Alert the IT Security team. Report any suspicious email (do not forward the email, instead ‘attach’ it to the new email).
- Update password: If you’ve realised you have given away personal information or credentials, seek support and ensure the password is changed immediately.
- Alert others. Let your colleagues and friends know so they are aware and not caught in the same trap.
